
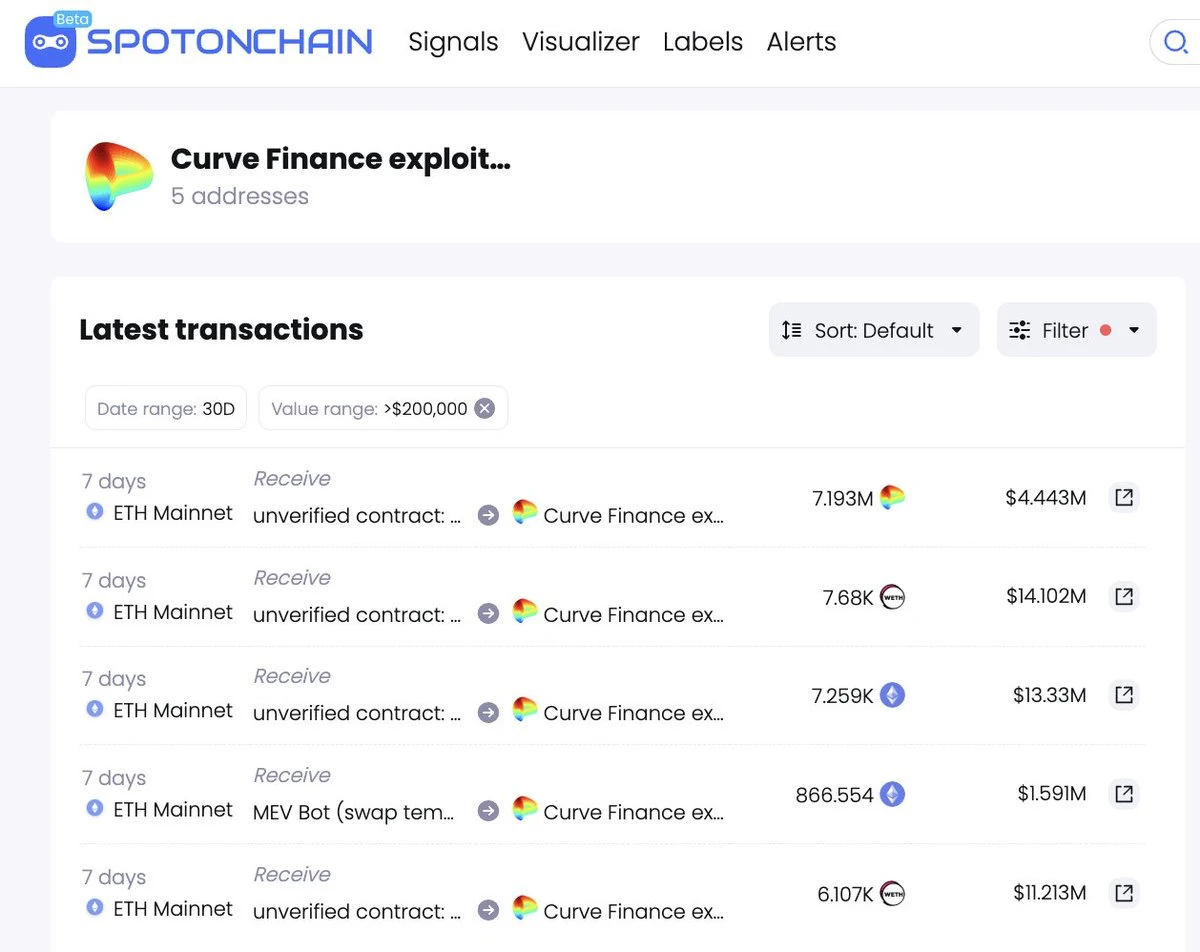
On July 30th, due to a recursive lock vulnerability in certain versions of Vyper (0.2.15, 0.2.16, and 0.3.0), the Curve stablecoin pools for alETH/msETH/pETH were attacked. As a result of the attack on some of Curve’s stablecoin pools, Alchemix, JPEG’d, Metronome, deBridge, and Ellipsis have currently suffered a cumulative loss of approximately $70 million:
-
Alchemix: 7,259 ETH and 4,821 alETH (approximately $22 million);
-
JPEG’d: 6,106 ETH (approximately $11.4 million);
-
Metronome: 866.554 ETH (approximately $1.6 million) and 955 smETH (approximately $1.7 million);
-
CRV-ETH pool: 10,500 ETH (approximately $19.4 million) and 7.19 million CRV (approximately $4.4 million).
Affected by the attack, CRV price drops, founder’s borrowed position faces liquidation risk
As a result of the attack, on July 31st, Curve Finance’s Total Value Locked (TVL) has dropped from $3.266 billion on July 30th to $1.869 billion, with a 24-hour decrease of 42.78%. The CRV price has also dropped by 14.89% in the past 24 hours.
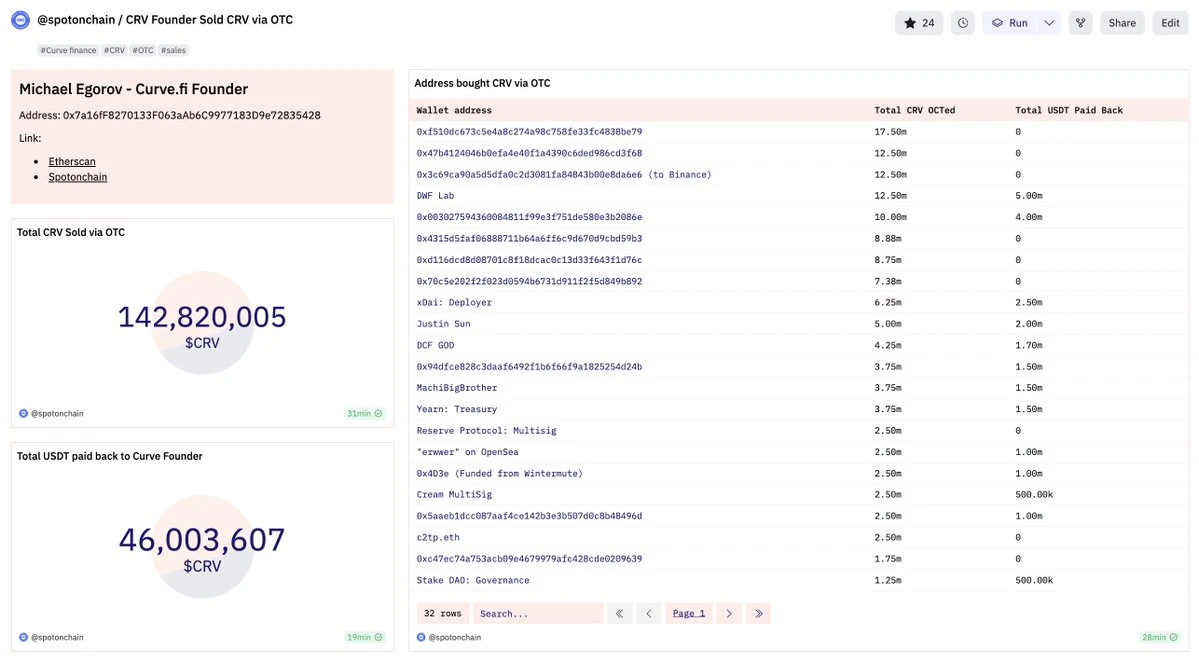
The downward trend in CRV price has forced Curve founder Michael Egorov’s borrowed position of $70 million on Aave to face liquidation risk. In view of this, Egorov has been selling CRV over the counter (OTC) to repay the loan.
Since the start of the OTC sales on August 1st, as of August 6th, Egorov has sold a total of 142.65 million CRV to 30 investors/institutions, exchanging them for $57.06 million.
As of August 6th, Egorov still has 269.8 million CRV (equivalent to $166 million) collateralized on four platforms, with a debt size of approximately $48.7 million.
Attacker returns funds
On July 30th, the exploit user coffeebabe.eth returned 786 ETH ($1.45 million) and 955 smETH ($1.74 million) to Metronome, and returned 2,879 ETH ($5.36 million) to Curve Finance;
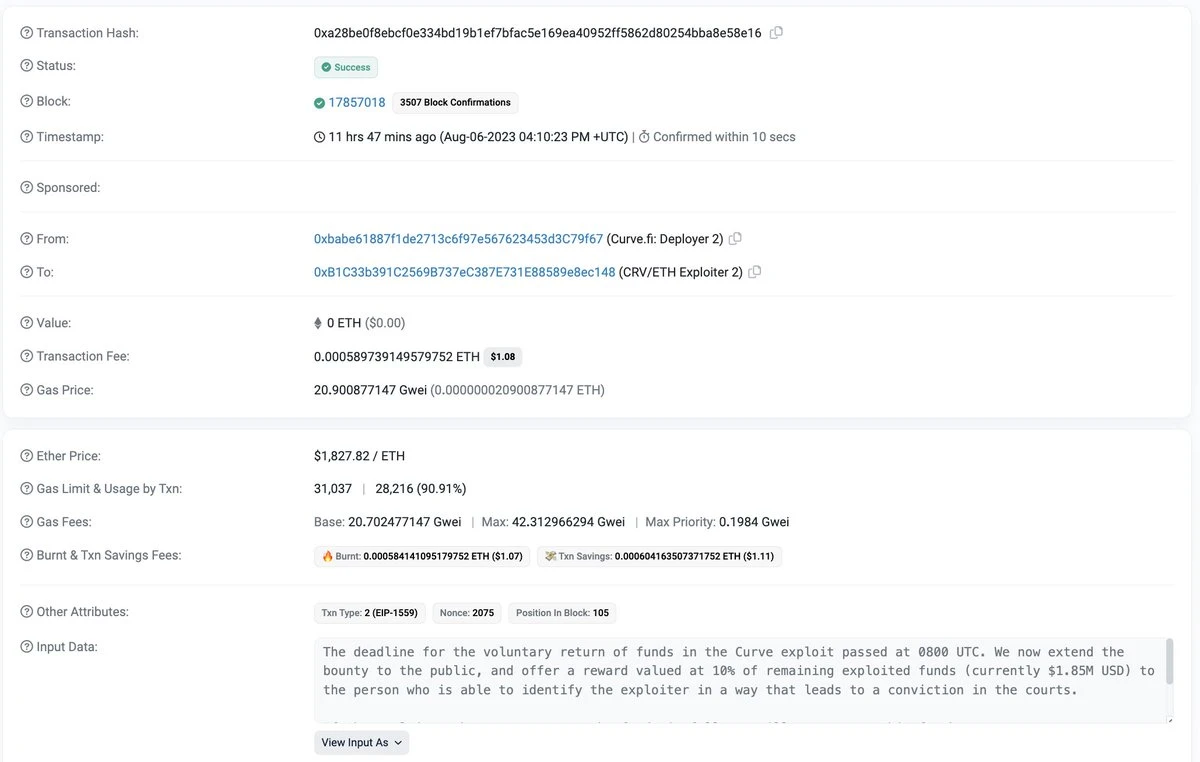
On August 3rd, the Curve Foundation sent an on-chain message to the exploit user, stating that if the attacker returns the remaining 90% before 8 a.m. (UTC) on August 6th, they will receive 10% of the stolen funds as a bounty;
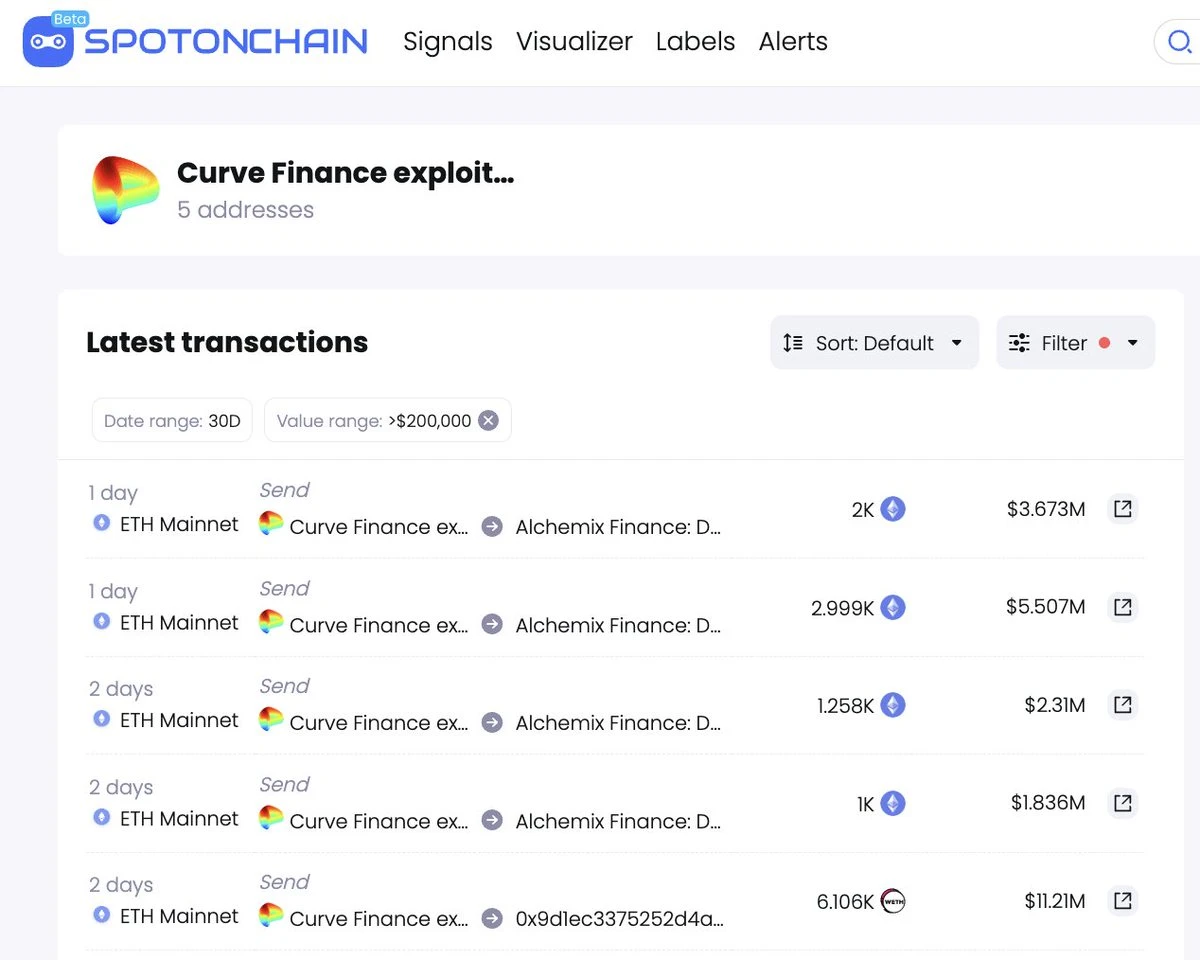
On August 4th, the attacker 0x6ec returned 5,495 WETH ($10 million) to JPEG’d and kept 610 ETH ($1.1 million) as a 10% bounty; the attacker 0xdce returned 2,258 ETH ($4.15 million) and 4,820 alETH ($8.82 million) to AlchemixFi;
On August 5th, 0xdce returned 4,999 ETH ($9.18 million) to AlchemixFi, all of which has been returned;
On August 6th, 32% of the stolen assets ($18.7 million) have not been returned:
-
80 ETH ($14,700) from MetronomeDAO (held by coffeebabe.eth);
-
7,681 ETH ($14.4 million) and 7.19 million CRV ($4.43 million) from the CRV-ETH pool.
As of the time of writing, out of the $59.5 million stolen in the Curve Finance Vyper exploit, approximately $40.3 million has been returned, $560,000 is being offered as a reward for the hacker, and approximately $18.7 million has not yet been returned by the CRV/ETH exploiters (0xb752…b324).
On August 7th, Curve Finance tweeted that the deadline for the voluntary return of funds by the CRV/ETH exploiters has passed, and a reward will be provided for anyone who provides information leading to the arrest and conviction of the hacker (currently $1.85 million).
In addition, Odaily Daily Planet warns that there have been some accounts impersonating Curve officials on X (i.e., Twitter) recently. Scam accounts often have blue or yellow markings, so caution is advised.
Like what you're reading? Subscribe to our top stories.
We will continue to update Gambling Chain; if you have any questions or suggestions, please contact us!