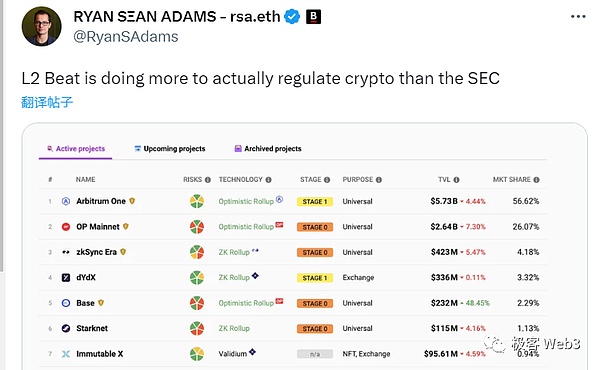
When it comes to the name L2BEAT, most people may have heard of it, but they don’t know much about what it does. For a long time before 2023, people’s impression of L2BEAT was often just “the data visualization platform for Ethereum Layer2”. Apart from displaying TVL data and categorizing technical solutions in the L2 track, not many people seem to understand the functionality of L2BEAT. However, with the gradual rise of the Layer2 risk rating index launched in June this year, L2BEAT, a niche organization comparable to a “Ethereum L2 rating agency”, has become known to more and more people.
When it comes to the term “rating agency”, the book “The World Is Flat” once had a vivid metaphor: “We live in a world of two superpowers, one is the United States and the other is rating agencies. The United States can destroy a country with bombs, and rating agencies can destroy a country by downgrading its bonds; sometimes, it is hard to say which one is more powerful.”
From the Asian financial crisis in 1997 to the subprime mortgage crisis in 2007, Wall Street rating agencies played a crucial role and even became important catalysts for these catastrophic events. In the Web3 circle, which emphasizes “decentralization” on the surface but relies on “social consensus” in practice, “risk rating” is an important aspect that cannot be bypassed. Whether it is contract code audits or on-chain anomaly analysis, their value is no less than zero-knowledge proofs and consensus algorithms, or even surpasses them.
- LianGuai Morning Post | US SEC accuses Hawaiian man of implementing a false cryptocurrency pump and dump scheme
- Weekly Announcement | Connext will airdrop its native token Next on September 5th; ImmutableX (IMX) unlocks tokens worth nearly tens of millions of dollars.
- People’s Court Daily Identification of the Property Nature of Virtual Currency and Issues Regarding the Disposal of Assets Involved in Cases (Full Text)
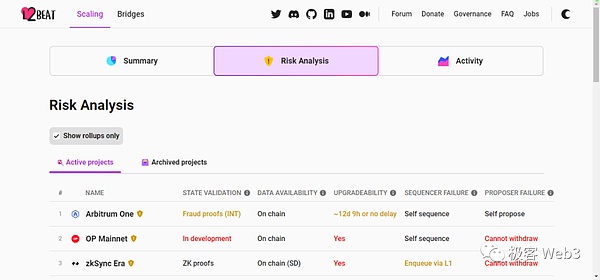
For the new field of modular blockchains, a set of objective, comprehensive risk assessment indicators that can differentiate different Layer2 solutions is particularly important. Especially in the current L2 ecosystem, which has supported nearly billions of dollars in assets, how to better identify potential risks in L2 and provide better warnings to the public has become an unavoidable reality.

In a forum blog post in 2022, Vitalik mentioned that almost all Rollups are not mature yet and most of them use auxiliary measures called Training Wheels to ensure the normal operation of Rollups. “Training Wheels” reflects the extent to which the Rollup project relies on “human intervention” and “social consensus”. The less dependent on auxiliary measures, the more “decentralized” the L2 is and the lower the risk; otherwise, the higher the risk.
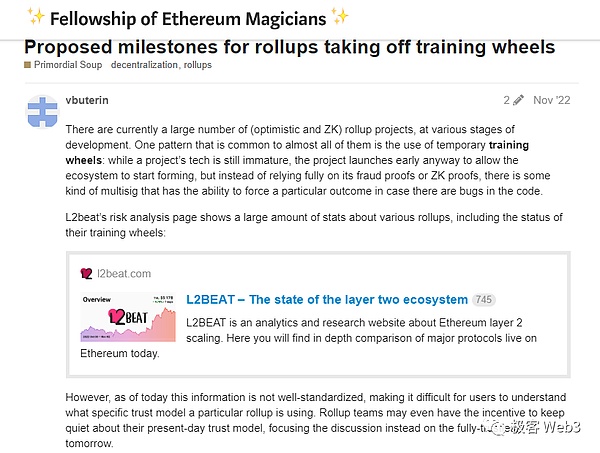
For example, optimistic Rollups, including Optimism, mostly do not have fraud-proof systems, which greatly increases the risk level. There are also many L2 solutions like Immutable X that implement data availability (DA) off-chain from the ETH chain, or lack features like the ability to withdraw funds or force transactions on demand, similar to Starknet. These conditions are necessary to ensure that Layer2 is “equivalent to the security of ETH”. Of course, besides these, almost all L2 projects have left themselves a “backdoor” by relying on a set of multisig to manage the contract code of L2 on Ethereum and can change the state hash at any time, which is also a huge risk.

In order to better differentiate and define Rollup, Vitalik and others divided Rollup into three levels, namely Stage 0, Stage 1, and Stage 2, based on the degree of dependence on auxiliary wheels/artificial intervention in a Rollup project. Later, L2beat revised this classification scheme through community feedback, which can be summarized as follows:
Stage 0 – Completely dependent on auxiliary wheels, the minimum standards that a Rollup should meet:
·The project claims to be a Rollup.
·The transactions processed by the Rollup should be “on-chain” (the data involving the L2 state transition process should be disclosed to L1, and the hash stateroot of the L2 state should also be disclosed;)
·There should be a batch of permissioned and open-source Rollup full nodes that can help users obtain the state of all accounts on L2 (including balances, transaction counts, etc.).
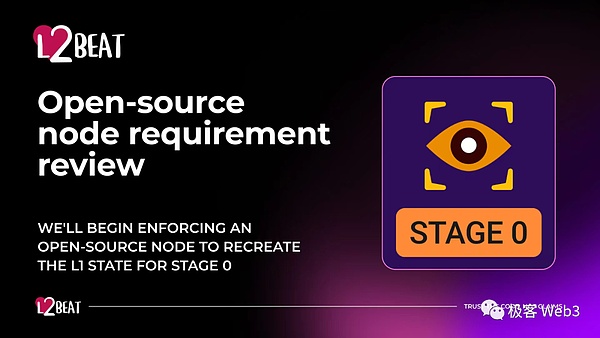
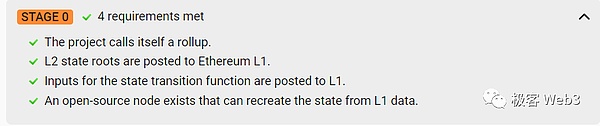
L2 projects that meet all of the above conditions will be marked as Stage 0 by L2beat, which is the minimum standard for a Rollup. Otherwise, it will not be considered a Rollup (such as Arbitrum Nova).

Stage 1 – Rollup partially dependent on auxiliary wheels, which have the following characteristics:
·Must implement fraud proof/validity proof systems to ensure the validity of L2 state transitions;
·If it is an optimistic Rollup, there must be at least 5 non-officially controlled L2 nodes that can publish fraud proofs (the challenger whitelist must include at least 5 entities outside of the Rollup official).
For example, as of November 2022, the challenger whitelist members of Arbitrum One include 9 entities: Consensys, Ethereum Foundation, L2BEAT, Mycelium, Offchain Labs, P2P, Quicknode, DLRC, Unit410.

·At any time, users can bypass the sequencer (operator) and forcefully withdraw assets on L2 to L1 to ensure that assets will not be frozen; if the sequencer launches a censorship attack and refuses to process certain transactions, users can forcefully submit the transactions to the Rollup transaction sequence on L1. Apart from publishing incorrect stateroots, the sequencer cannot engage in other malicious behaviors.
·Rollup can set up a security committee managed by a group of multisignatures, which has the power to forcibly upgrade the Rollup contract in emergency situations or intervene in the L2 state hash recorded on the contract. However, the multisignature private keys of the committee must be sufficiently decentralized and the threshold must be high enough. Vitalik himself believes that this value should be at least 6/8, which means that the multisignature is managed by more than 8 people, and the effective threshold is 75%.
·Rollup contracts that are not authorized by the committee’s multi-signature are subject to a time lock delay of at least 7 days. This way, if the Rollup encounters malicious update proposals such as governance attacks (referencing the Tornado Cash governance attack incident), users will have at least 7 days to safely withdraw their funds.
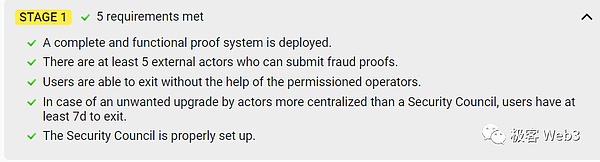
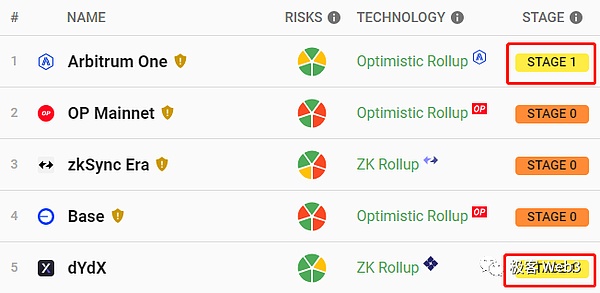
Currently, only Arbitrum One, dYdX, zkSync Lite have reached Stage 1 requirements among mainstream Rollups, while other mainstream Rollups remain at Stage 0.
Stage 2 – Completely abandon auxiliary chains and become a full-fledged Rollup:
·Optimistic Rollup networks should have L2 nodes that can publish fraud proofs as Permissionless, eliminating whitelist settings (Arbitrum One recently released a protocol called BOLD for this purpose);
·All Rollup contract upgrades should be subject to a time lock delay of at least 30 days, or they should simply be unable to upgrade contracts. This means that if a malicious upgrade occurs, L2 users will have at least 30 days to safely withdraw their funds.
In order to better understand the risk rating indicators listed by L2BEAT, we can analyze three Rollup instances with different security levels.
Stage 0 – Base, Stage 1 – Arbitrum One, Stage 2 – Fuel:
Base is one of the leading projects in the Optimistic Rollup track. It uses contracts on L1 to record the L2 state hash (Stateroot), process funds entering and exiting L2, and achieve data availability (DA) with Ethereum through bridging.
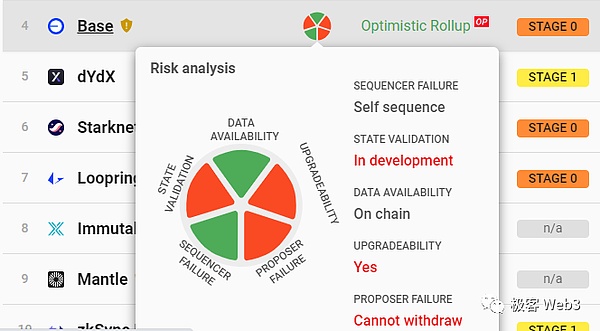
The Base sequencer needs to disclose L2 transaction data to L1. Specifically, the sequencer initiates a transaction to a specified address on Ethereum every few minutes. In the transaction’s customizable additional data (Calldata), a batch of compressed transaction data is recorded. Since L2 full nodes automatically sync L1 blocks, they can monitor this transaction initiated by the sequencer and parse the L2 transaction data from its Calldata, thereby obtaining the latest state of the L2 sequencer and calculating the correct state hash (Stateroot) to compare with the Stateroot submitted by the sequencer on L1.
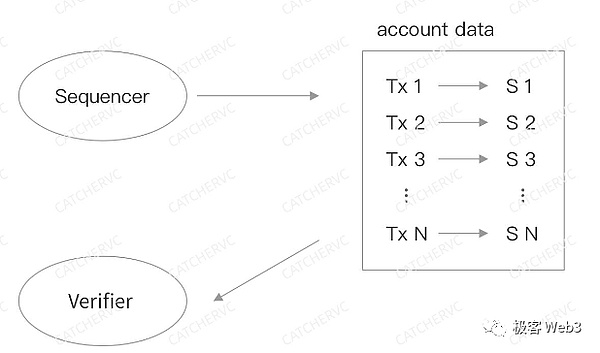
Currently, Base does not have a fraud proof system to guarantee that the L2 Stateroot recorded in the L1 contract is correct. However, users who have the capability to run L2 full nodes can promptly identify any errors. In addition, Base does not have a solution to resist censorship attacks such as mandatory withdrawals. If the sequencer is down for a long time or deliberately refuses user requests, L2 users will be unable to safely withdraw their funds to L1, so there are significant security risks.
Obviously, such a Rollup is not secure at the mechanism design level. However, users and members of the L2 community can issue warnings through social media when necessary, making the Ethereum Foundation and even regulatory bodies such as the SEC aware of the dangers. This is known as “social consensus”, which restricts malicious behavior by L2 project teams through high data transparency and community self-monitoring, using “public opinion fermentation”, “human intervention”, and subsequent “legal accountability”. It is the lowest level of security guarantee because it cannot prevent malicious behavior in advance, but can only hold the responsible parties accountable after the fact.
But in fact, “social consensus” is also the basic condition for ensuring the security of the blockchain (if someone tries to maliciously fork Ethereum, the Ethereum community will also determine through social consensus which forked chain should be followed), and malicious actors are mostly unwilling to take risks considering the consequences of their actions being exposed (except for exchanges like FTX, ZT, and Mentougou).
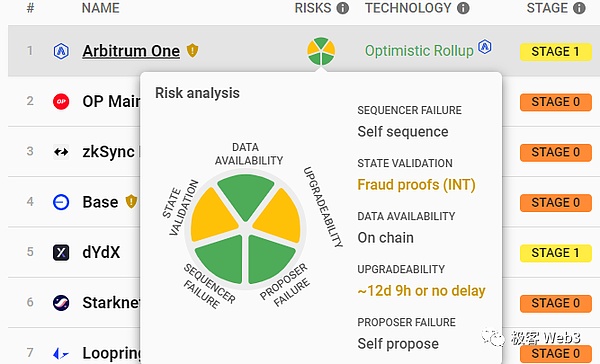
When we change the subject of investigation to Arbitrum One, we can immediately see the differences between it and Base. For example, it has launched a usable fraud proof system and set up a challenger whitelist, which includes 9 different entities running nodes, including the Ethereum Foundation and L2beat. As long as the sequencer publishes the wrong state hash Stateroot to L1, the challenger node will publish a fraud proof to ensure that the L2 Stateroot recorded in the Rollup contract is correct;
At the same time, Arbitrum One has a mandatory transaction mechanism to deal with sequencer censorship attacks, which allows users to call the force inclusion function of the Sequencer Inbox contract on L1 to directly submit transaction instructions to L1; if within 24 hours, the sequencer does not process the transaction/withdrawal that needs to be “force included”, the transaction/withdrawal instruction will be directly included in the Rollup transaction sequence, thus creating a “secure exit” for users to force withdrawal from L2.
It needs to be emphasized that in Stage 1 Rollup projects, as long as users can obtain the overall account state of L2 and construct a Merkle Proof corresponding to their account balance, they can force withdrawals through the designated function in the Rollup contract (this function is generally called the escape hatch). As for how to obtain the account state on L2, it depends on whether there are full nodes in the Rollup network that open data to the outside world (almost all L2 networks have such nodes).
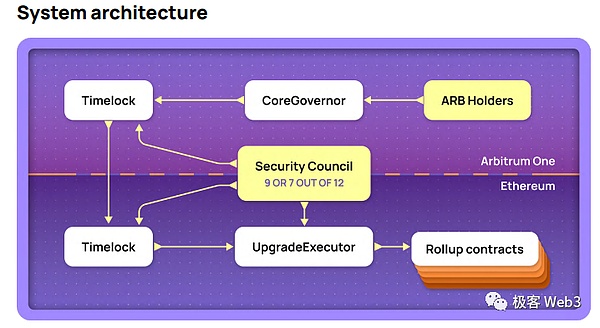
In addition, the contract upgrade behavior of Arbitrum One is subject to various restrictions, such as: normal contract upgrade proposals must first pass the on-chain governance vote decision, once the voting threshold is passed, it will be subject to a time lock restriction (with a delay of 12 days), and then it will be automatically executed. If the contract upgrade proposal contains malicious code logic, it can be vetoed by the safety committee (executed through multi-signature).
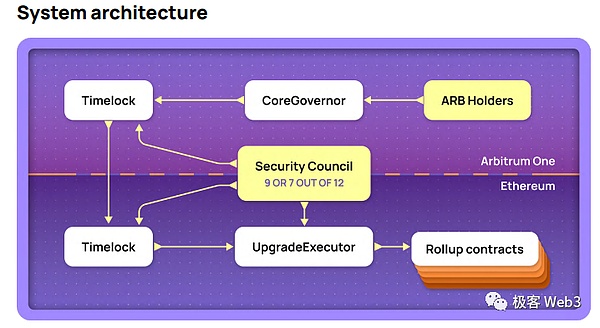
However, the Arbitrum One safety committee can bypass the time lock restrictions, for example, as long as 9/12 multi-signatures are passed, the safety committee can immediately upgrade the contract code or forcibly change the L2 Stateroot recorded in the Rollup contract.
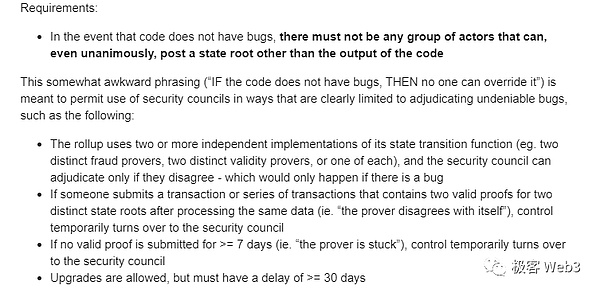
As for why the safety committee has such great power, Vitalik explained it as follows:
“Some Rollups may adopt multiple independent state transition functions, such as having two fraud proof publishers with different views, or multiple Prover nodes submitting different validity proofs, or the sequencer attempting to fork the L2 ledger on L1, or the validity proof not being submitted on-chain within 7 days, all of which may cause the L2 system to collapse completely. The safety committee can make judgments in such dangerous situations and guide the system to adopt the correct result through manual intervention.“
Of course, Vitalik only listed a few simple “dangerous situations”. Considering that Rollup contracts may be attacked by hackers and sorters may be compromised (or have insiders), it is obviously necessary to take emergency measures.
According to Vitalik, for a perfect Rollup, the contract can be upgraded, but there must be a time lock delay of more than 30 days to give users and community members enough time to react.
Obviously, because Arbitrum’s security committee can immediately upgrade the contract after multi-signature approval, if the new version of the code contains malicious business logic, theoretically, it can take away users’ assets on L2. So Arbitrum One does not meet Vitalik’s definition of a perfect Rollup, it is just a lower level of risk.
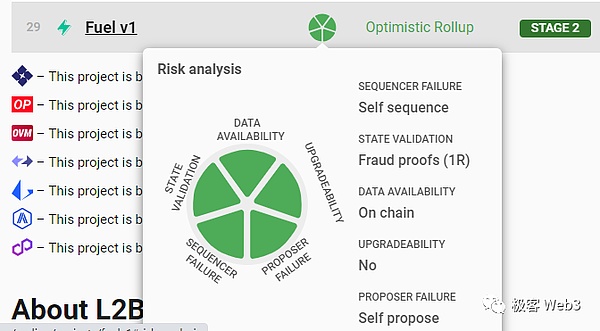
When we consider a “perfect Rollup”, there are only two projects on L2BEAT that meet the criteria: Fuel V1 and DeGate. Among them, Fuel V1 is the first optimistic Rollup to implement a fraud proof system. Its fraud proof submission is permissionless, and anyone can run a node and submit a fraud proof when necessary. At the same time, Fuel V1’s contract is hardcoded and cannot be upgraded, and the committee cannot intervene in the L2 Stateroot recorded on the Rollup contract, so there is no so-called security committee risk.
Fuel V1 achieves the lowest level of risk, but each update iteration requires redeploying the contract and users need to manually migrate their assets to the new version, essentially creating a new project. This results in fragmented liquidity and greatly reduces flexibility. Due to reasons such as using UTXO as the programming model instead of being compatible with EVM and the founder later joining the Celestia team, Fuel’s development has gradually stagnated and ecosystem construction has been unsatisfactory.
In summary, pursuing absolute security comes at the cost of inconvenience in updates and iterations, and in the current situation where fraud proof and validity proof technologies are not yet perfect, maintaining a certain level of contract upgradeability may be a necessary feature of Rollups.
In the foreseeable future, most Rollups will not give up on security committee multi-signatures, and L2 contracts will have “immediate upgradeability” for a long time (a certain ZK Rollup project has never given up on security committee multi-signatures and later turned to create a new project directly). Given the difficulty of developing fraud proof systems, most non-leading optimistic Rollups may not be able to implement fraud proofs in the short term (it is unlikely that they will be able to do so by the end of 2023), while Arbitrum One will maintain a leading position in the Rollup race for a long time. Although it does not have the highest level of security, it has a relatively complete fraud proof system, security committee multi-signatures are reasonably distributed (9 out of 12 multi-signatures are allocated to 12 community members, including ARB project team members), and it also has the largest DApp ecosystem with over 440 applications. As for Base, which has poor security and relies more on marketing, whether it can sustain the growth momentum of the past few months remains to be seen. If Base’s TVL volume can surpass Arbitrum One, it may lead to the collapse of the belief in “decentralization” itself.
Of course, the most important thing is that we will always need risk rating agencies like L2BEAT. In this turbulent and chaotic era, a set of clear and comprehensive risk rating indicators is always the key to ensuring the vibrant development of the Ethereum system and the entire Web3.
Like what you're reading? Subscribe to our top stories.
We will continue to update Gambling Chain; if you have any questions or suggestions, please contact us!