Author: TechFlow Butcher
It’s shocking to say that in a leaked video, Vitalik Buterin, co-founder of Ethereum, stated that every Layer 2 and Rollup (scaling solution) on Ethereum has a backdoor for developers to enter and make changes when necessary.
Vitalik said he has discussed this with the upgrade team and “what they want to do next year is start taking off the training wheels.”
There are two different opinions about this statement.
- Decoding Rollup Economics How is revenue currently generated? Can we build a Rollup Alliance in the future to achieve interoperability?
- What types of projects are worth long-term investment?
- Roadmap for GMX v2 How to promote the adoption of GM?
Some believe that the existence of the “backdoor” mechanism is not a secret and can be understood and accepted.
This practice has been in place since The DAO was hacked in 2016 because smart contract vulnerabilities can have devastating consequences.
Most of the L2 protocols currently running on Ethereum have only been around for a few months, so bugs are expected for such new protocols. Therefore, smart contract developers often implement a mechanism that allows freezing, upgrading, and even reversing changes to contracts in certain situations.
For a new Dapp or protocol, launching without some fault-tolerant mechanisms is too risky because audits can’t guarantee that there won’t be vulnerabilities.
Therefore, it’s not surprising that these L2 solutions have these mechanisms. They are currently centralized in other aspects, such as sequencers, but the ultimate goal is still decentralization, which is always a process that can be understood.
However, some people are not buying it and believe that Ethereum’s decentralization is nothing but a lie.
For example, in response to Vitalik’s remarks, Chris O, a community leader of the public chain Cardano, tweeted that Vitalik’s words exposed that Ethereum is not as immutable, permissionless, or resistant to censorship as people think, and took the opportunity to praise ADA.
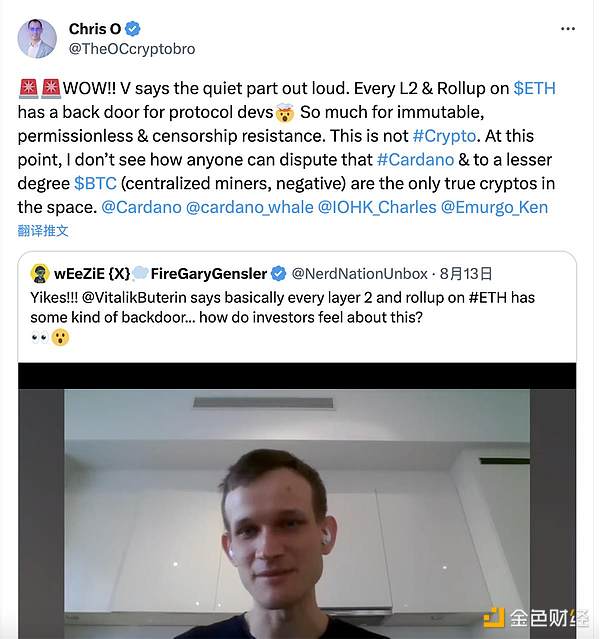
“Ethereum is not a true cryptocurrency. On this point, I don’t think anyone would question that Cardano and Bitcoin (which are less centralized) are the only true cryptocurrencies in this field.”
In Ethereum’s past practices, there is a mechanism for upgrading through forks to address security issues. However, this kind of upgrade is done in a decentralized manner, where nodes can choose whether to upgrade, and an upgrade cannot be completed without the consent of the majority of forkers and node operators.
But in Layer 2, there is no decentralized fork upgrade mechanism, which creates a dilemma. Without an upgrade mechanism, removing this “backdoor” can be said to be too risky, but it does contradict the principle of decentralization.
Similar to Tether and Circle behind USDT and USDC, they can freeze USDT and USDC in the event of a major security incident to save stolen assets. It is estimated that the project team also hopes to have control over the key to the fate of L2.
“After all, security is better in a centralized system.”
Like what you're reading? Subscribe to our top stories.
We will continue to update Gambling Chain; if you have any questions or suggestions, please contact us!