Author:
Jesse_meta, Researcher at SUSS NiFT (Inclusive Finance Node) at XinYue University
EatonAshton2, Researcher at Beosin
kaplannie, Security Researcher at Least Authority
- An In-depth Explanation of Friend Tech’s Economic Model Game Theory, Expected Value, and Demand Curve
- Friend.tech Economic Model in Detail The Illusion of Game Theory, Expected Value, and Demand Curve
- MetaMask Snap Technology Interpretation Development Experience, Capability Limitations, Security, and Business Potential Analysis
Whether information is stored on the Internet or in offline archives, whether it is due to subjective intent or objective accidents, information leakage incidents are common today and do not need to be elaborated. As long as information is stored in a centralized manner, there is a risk of being attacked at a single point. As long as the verification process requires a trusted third party, there is a moral risk and inefficiency. The solution to information security is of utmost importance and urgent. Zero-knowledge proof technology allows users to complete verifications more efficiently and securely while protecting their privacy.
If Bitcoin is the first major invention brought by blockchain to the real world, providing a new way of value storage, and Ethereum’s smart contracts are the second major milestone event, unlocking the potential for innovation, then the application of zero-knowledge proofs is the third major technological innovation in the history of blockchain development, bringing privacy and scalability. This is not only an important part of the Web3 ecosystem, but also an important foundational technology with the potential to drive social change.
This article, from the perspective of non-technical personnel, introduces the application scenarios, working principles, development status, and future trends of zero-knowledge proofs, in order to help readers without technical backgrounds understand the significant changes that zero-knowledge proofs are about to bring.
1. What is Zero-Knowledge Proof
Zero-knowledge proof (ZKP) is a mathematical protocol first proposed in 1985 by Shafi Goldwasser, Silvio Micali, and Chales Rackoff in their paper “The knowledge complexity of interactive proof systems”. Besides proving a certain fact, it does not reveal any other information. The verifier cannot obtain the secret information used to generate the proof. Let’s use an example to help everyone understand: I want to prove that I know someone’s phone number, I only need to be able to dial that person’s phone in front of everyone to prove this fact, without revealing the person’s real number. Zero-knowledge proofs provide an effective and almost risk-free way of sharing data. By using zero-knowledge proofs, we can retain ownership of the data, greatly enhance privacy protection, and potentially make data leakage incidents a thing of the past.
Zero-knowledge proofs have three characteristics:
Completeness
If a statement is true, an honest verifier will be convinced by an honest prover. In other words, the right thing cannot be wrong.
Soundness
If a statement is false, in most cases, a deceitful prover cannot make an honest verifier believe in a false statement. In other words, the wrong thing cannot be right.
Zero-knowledge
If a statement is true, the verifier can only know that the statement is true and cannot obtain any additional information.
Zero-knowledge proofs have a very small probability of producing soundness errors, that is, a cheating prover may make an honest verifier believe in a false statement. Zero-knowledge proofs are probabilistic proofs, not deterministic proofs, but we can use some techniques to reduce the soundness error to a negligible level.
2. Applications of Zero-Knowledge Proofs
The two most important applications of zero-knowledge proofs are privacy and scalability.
2.1 Privacy
Zero-knowledge proofs allow users to securely share necessary information to obtain goods and services without revealing their personal details, protecting them from hacker attacks and identity theft. As the digital and physical worlds merge, the privacy protection provided by zero-knowledge proofs becomes crucial for Web3 and beyond. Without zero-knowledge proofs, user information would be stored in trusted third-party databases, exposing them to potential hacking risks. The first use case of zero-knowledge proofs in blockchain is the privacy coin Zcash, which hides transaction details.
2.1.1 Protection and Verification of Identity Information
In online activities, we often need to provide personal information such as name, date of birth, email, and complex passwords to prove that we are legitimate users. As a result, we often leave behind sensitive information that we are reluctant to disclose online. Nowadays, receiving fraudulent phone calls addressing us by our name is not uncommon, highlighting the serious issue of personal information leakage.
We can utilize blockchain technology to give each individual a unique encrypted digital identifier that contains their personal data. This digital identifier can establish a decentralized identity that cannot be forged or altered without the owner’s knowledge. Decentralized identities can be controlled by users to grant access to personal identity, simplifying the authentication process and reducing incidents of users losing access due to forgotten passwords. Zero-knowledge proofs are generated from public data that can prove user identity and private data containing user information, which can be used for identity verification when accessing services. This reduces cumbersome verification processes, improves user experience, and avoids centralized storage of user information.
In addition, zero-knowledge proofs can be used to build private reputation systems, allowing service providers to verify if users meet certain reputation criteria without exposing their identities. Users can anonymously output reputations from platforms such as Facebook, Twitter, and Github without revealing the specific source accounts.
2.1.2 Anonymous Payments
Transaction details made with bank cards are usually visible to multiple parties, including payment providers, banks, and governments, exposing the privacy of ordinary citizens. Users have to trust these parties not to misuse the information.
Cryptocurrencies enable payments to be conducted peer-to-peer without intermediaries. However, transactions on mainstream public chains are publicly visible, and although user addresses are anonymous, it is still possible to find real-world identities through on-chain correlated addresses and off-chain data analysis, such as KYC in exchanges and Twitter information. Knowing someone’s wallet address is equivalent to being able to view their bank account balance at any time and can even pose a threat to their identity and property.
Zero-knowledge proofs can provide anonymous payments at three levels: privacy coins, privacy applications, and privacy public chains. Privacy coin Zcash hides transaction details, including sender and recipient addresses, asset type, quantity, and time. Tornado Cash is a decentralized application on Ethereum that uses zero-knowledge proofs to obfuscate transaction details for private transfers (although it is also often used for money laundering). Aleo is an L1 blockchain designed to provide privacy features for applications at the protocol level.
2.1.3 Honest behavior
Zero-knowledge proofs can facilitate honest behavior while preserving privacy. The protocol may require users to submit zero-knowledge proofs to demonstrate their honesty. Since the validity of zero-knowledge proofs cannot be falsified, users must engage in honest behavior according to the protocol requirements in order to submit valid proofs.
MACI (Minimal Anti-Collusion Infrastructure) is an application scenario that promotes honesty and prevents collusion in on-chain voting or other decision-making processes. This system utilizes key pairs and zero-knowledge proof technology to achieve this goal. In MACI, users register their public keys in a smart contract and send their votes to the contract through encrypted messages. The anti-collusion feature of MACI allows voters to change their public keys to prevent others from knowing their voting choices. Coordinators use zero-knowledge proofs to demonstrate that they have correctly processed all messages at the end of the voting period, and the final voting result is the sum of all valid votes. This ensures the integrity and fairness of the voting process.
2.1.4 Personal information verification
When we want to obtain a loan, we can obtain a digital income certificate from a company to apply for the loan. The validity of this certificate can be easily verified using cryptography. Banks can use zero-knowledge proofs to verify whether our income meets the specified minimum requirements without obtaining sensitive specific information.
2.1.5 Exploring the potential of private data through machine learning
When training machine learning models, a large amount of data is usually required. By using zero-knowledge proofs, data owners can prove that their data meets the requirements for model training without actually disclosing the data. This enables private data to be utilized and monetized.
In addition, zero-knowledge proofs can allow model creators to prove that their models meet certain performance indicators without disclosing the details of the models, to prevent others from copying or tampering with their models.
2.2 Scalability
As the number of blockchain users increases, a large amount of computation is required on the blockchain, resulting in transaction congestion. Some blockchains take the sharding route for scalability, but this requires complex modifications to the underlying layer of the blockchain, which may threaten the security of the blockchain. Another feasible solution is to take the ZK-Rollup route, using verifiable computation to outsource the computation to entities on another chain, and then submit the zero-knowledge proofs and verifiable results to the main chain for authenticity verification. Zero-knowledge proofs ensure the authenticity of transactions, and the main chain only needs to update the results to the state without storing details or replaying computations, or waiting for others to discuss the authenticity of transactions, greatly improving efficiency and scalability. Developers can leverage zero-knowledge proofs to design lightweight dapps that can run on ordinary hardware such as smartphones, making it more accessible for Web3 to reach the masses.
The scalability of zero-knowledge proofs can be applied to both layer-one networks, such as Mina Protocol, and layer-two networks like ZK-rollups.
3. How Zero-Knowledge Proofs Work
Dmitry Laverenov (2019) divides the structure of zero-knowledge proofs into interactive and non-interactive.
3.1 Interactive Zero-Knowledge Proofs
The basic form of an interactive zero-knowledge proof consists of three steps: evidence, challenger, and response.
Evidence: The hidden secret information is the evidence of the prover. This evidence establishes a series of questions that can only be answered correctly by someone who knows this information. The prover randomly selects a question and sends the computed answer to the verifier for proof.
Challenger: The verifier randomly selects another question from the set and challenges the prover to answer.
Response: The prover accepts the question, computes the answer, and returns the result to the verifier. The prover’s response enables the verifier to check whether the prover knows this evidence.
This process can be repeated multiple times until the probability of the prover guessing the correct answer without knowing the secret information becomes sufficiently low. Taking a simplified mathematical example, if the probability of the prover guessing the correct answer without knowing the secret information is 1/2, and the interaction is repeated ten times, the probability of the prover hitting the correct answer each time is only 0.0097%, making it highly unlikely for the verifier to mistakenly accept a false proof.
3.2 Non-Interactive Zero-Knowledge Proofs
Interactive zero-knowledge proofs have limitations. On one hand, they require the presence of both the prover and the verifier to repeatedly verify. On the other hand, each computation of a new proof requires the prover and the verifier to exchange a set of information, and the proof cannot be reused in independent verifications.
To address the limitations of interactive zero-knowledge proofs, Manuel Blum, LianGuaiul Feldman, and Silvio Micali proposed non-interactive zero-knowledge proofs, where the prover and the verifier share a key and only need one round of verification to make the zero-knowledge proof more efficient. The prover computes a zero-knowledge proof by using a special algorithm to generate the secret information and sends it to the verifier. The verifier uses another algorithm to check if the prover knows the secret information. Once generated, the zero-knowledge proof can be verified by anyone with the shared key and verification algorithm.
Non-interactive zero-knowledge proofs are a major breakthrough in zero-knowledge proof technology and have contributed to the development of zero-knowledge proof systems used today. The main methods include ZK-SNARK and ZK-STARK.
4. Main Technical Paths of Zero-Knowledge Proofs
Alchemy (2022) divides the technical paths of zero-knowledge proofs into ZK-SNARK, ZK-STARK, and Recursive ZK-SNARK.
4.1 ZK-SNARK
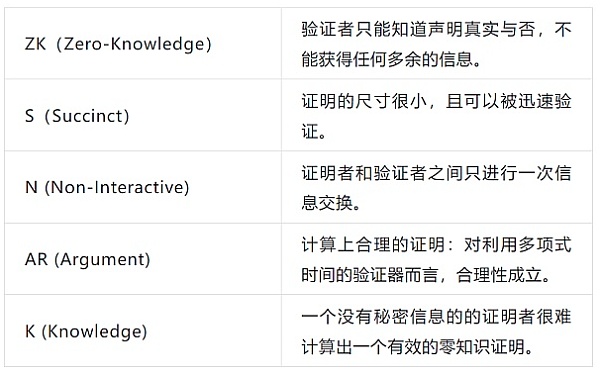
ZK-SNARKs are succinct non-interactive proofs of zero-knowledge.
Public blockchains need to ensure the correctness of transactions executed on the network by having other computers (nodes) re-run each transaction. However, this approach slows down the network speed and limits scalability as each node has to re-execute each transaction. Nodes also have to store transaction data, leading to exponential growth in the size of the blockchain.
For these limitations, ZK-SNARK comes into play. It can prove the correctness of computations performed off-chain without the need for nodes to replay every step of the computation. This also eliminates the need for nodes to store redundant transaction data, increasing network throughput.
Using SNARK to verify off-chain computations involves encoding the computation as a mathematical expression to form a proof of validity. Validators check the correctness of the proof. If the proof passes all checks, the underlying computation is considered valid. The size of the proof of validity is much smaller than the computation it verifies, which is why we call SNARKs succinct.
Most ZK Rollup solutions that use ZK-SNARK follow the following steps:
1. Users on L2 sign transactions and submit them to validators.
2. Validators compress multiple transactions using cryptography to generate corresponding proofs of validity (SNARKs).
3. Smart contracts on L1 verify the proofs of validity and determine whether this batch of transactions should be published to the main chain.
It is worth mentioning that ZK-SNARK requires a trusted setup. In this stage, a key generator obtains a program and a secret parameter to generate two usable public keys, one for creating proofs and one for verifying proofs. These two public keys only need to be generated once through a trusted setup ceremony and can be used multiple times by parties wishing to participate in zero-knowledge protocols. Users need to trust that the participants in the trusted setup ceremony will not act maliciously and that there is no way to evaluate the honesty of the participants. Knowing the secret parameter allows the generation of false proofs to deceive validators, so there is a potential security risk. Currently, researchers are exploring schemes for ZK-SNARK without the need for trusted assumptions.
Advantages
1. Security
ZK rollup is considered a more secure scaling solution compared to OP rollup because ZK-SNARK uses advanced cryptographic security mechanisms, making it difficult to deceive validators and engage in malicious behavior.
2. High Throughput
ZK-SNARK reduces the computational load on the Ethereum base layer, alleviating congestion on the mainnet. Off-chain computations share the transaction fees, resulting in faster transaction speeds.
3. Small Proof Size
The small size of SNARK proofs makes them easy to verify on the main chain, which means lower Gas Fees for verifying off-chain transactions, reducing costs for users.
Limitations
1. Relatively Centralized
Most of the time, it relies on a trusted setup, which contradicts the original intention of blockchain’s trustlessness.
Generating proofs of validity using ZK-SNARK is a computationally intensive process, and the prover must invest in specialized hardware. These hardware devices are expensive, and only a few people can afford them, making the proof generation process highly centralized.
2. ZK-SNARK uses elliptic curve cryptography (ECC) to encrypt the information used to generate proofs of validity, which is currently relatively secure. However, advancements in quantum computing may break its security model.
Projects that use ZK-SNARK
Polygon Hermez
Polygon acquired Hermez for $250 million in 2021, becoming the first case of comprehensive acquisition between two blockchain networks. The ZK technology and tools brought by Hermez to Polygon’s rapidly growing user base enable Polygon to support the development of zkEVM. Hermez 1.0 is a payment platform that executes a batch of transactions off-chain, allowing users to easily transfer ERC-20 tokens from one Hermez account to another, with a transaction speed of up to 2000 per second.
Hermez 2.0, as a zero-knowledge zkEVM, transparently executes Ethereum transactions, including smart contracts with zero-knowledge proofs. It is fully compatible with Ethereum, requiring minimal changes to smart contract code, making it convenient for developers to deploy L1 projects on Polygon Hermez. Hermez 1.0 uses SNARK-proofs, while 2.0 uses both SNARK-proofs and STARK-proofs. In 2.0, STARK-proofs are used to prove the validity of off-chain transactions. However, the cost of verifying STARK-proof on the main chain is high, so SNARK-proof is introduced to verify STARK.
zkSync
zkSync 1.0, launched by Matter Labs in 2020, does not support smart contracts and is mainly used for transactions or transfers. zkSync 2.0, which supports smart contracts, was publicly launched on the mainnet in March 2023.
zkSync compiles Solidity, the smart contract source code on Ethereum, into Yul to achieve EVM compatibility. Yul is an intermediate language that can be compiled into bytecode for different EVMs. The Yul code can be recompiled into custom, circuit-compatible bytecode for zkSync’s zkEVM design using the LLVM compiler framework. Through this approach, all steps in EVM execution are zk-verified without the need for proof by higher-level code, making the proof process more decentralized while maintaining high performance. In the future, support for Rust, JavaScript, or other languages can be added by building new compiler frontends, increasing the flexibility and developers of the zkEVM architecture.
Aztec
Aztec is the first hybrid zkRollup that enables the execution of both public and private smart contracts in one environment. It is a zero-knowledge execution environment, not zkEVM. By merging public and private execution into a single hybrid rollup, confidentiality is achieved, for example, privacy transactions of public AMMs, private conversations in public games, and privacy voting in public DAOs.
4.2 ZK-STARK
ZK-STARK does not require a trusted setup. ZK-STARK stands for Zero-Knowledge Scalable Transparent Argument of Knowledge. Compared to ZK-SNARK, ZK-STARK has better scalability and transparency.

Advantages
1. Trustlessness
ZK-STARK uses publicly verifiable randomness instead of a trusted setup, reducing reliance on participants and improving protocol security.
2. Stronger scalability
Even with exponential growth in the complexity of underlying calculations, ZK-STARK maintains low proof and verification times, unlike ZK-SNARK, which grows linearly.
3. Higher Security Guarantee
ZK-STARK uses collision-resistant hash values for encryption, instead of the elliptic curve scheme used in ZK-SNARK, which is resistant to attacks by quantum computing.
Limitations
1. Larger proof size
ZK-STARK has a larger proof size, making it more difficult to verify on the main network.
2. Lower adoption rate
ZK-SNARK is the first practical application of zero-knowledge proofs in the blockchain, so most ZK rollups adopt ZK-SNARK, which has more mature developer systems and tools. Although ZK-STARK also has support from the Ethereum Foundation, its adoption rate is lower and the underlying tools still need improvement.
Which projects use ZK-STARK?
Polygon Miden
Polygon Miden, an extension solution based on Ethereum L2, uses zk-STARK technology to integrate a large number of L2 transactions into a single Ethereum transaction, thereby improving processing capacity and reducing transaction costs. Without sharding, Polygon Miden can generate a block in 5 seconds, and its TPS can reach over 1000. After sharding, its TPS can reach up to 10,000. Users can withdraw funds from Polygon Miden to Ethereum in just 15 minutes. The core feature of Polygon Miden is a STARK-based Turing complete virtual machine, Miden VM, which makes formal verification of contracts easier.
StarkEx and StarkNet
StarkEx is a permissioned framework for customized extension solutions for specific applications. Projects can use StarkEx for low-cost off-chain computation and generate STARK proofs to verify the correctness of execution. Such proofs can contain 12,000-500,000 transactions. Finally, the proofs are sent to the on-chain STARK verifier for validation, and once validated, state updates are accepted. Applications deployed on StarkEx include perpetual options dYdX, NFT L2 Immutable, sports digital card trading platform Sorare, and multi-chain DeFi aggregator rhino.fi.
StarkNet is a permissionless L2 where anyone can deploy smart contracts developed in the Cairo language. Contracts deployed on StarkNet can interact with each other to build new composable protocols. Unlike StarkEx, where applications are responsible for submitting transactions, the StarkNet sequencer batches transactions and sends them for processing and proof generation. StarkNet is more suitable for protocols that require synchronization with other protocols or go beyond the scope of StarkEx applications. As StarkNet develops, applications based on StarkEx will be able to be ported to StarkNet and enjoy composability.
ZK-SNARK and ZK-STARK Comparison

4.3 Recursive ZK-SNARK
Ordinary ZK rollups can only handle one transaction block, which limits the number of transactions they can process. Recursive ZK-SNARK can verify more than one transaction block by merging the SNARKs generated by different L2 blocks into a single validity proof and submitting it to the L1 chain. Once the contract on the L1 chain accepts the submitted proof, all these transactions become valid, greatly increasing the number of transactions that can be completed using zero-knowledge proofs.
Plonky2 is a new proof mechanism for increasing transactions in Polygon Zero using recursive ZK-SNARK. Recursive SNARK extends the proof generation process by aggregating multiple proofs into a recursive proof. Plonky2 uses the same technique to reduce the time it takes to generate new block proofs. Plonky2 parallelizes the generation of thousands of transactions and recursively aggregates them into a block proof, resulting in fast generation speed. Traditional proof mechanisms attempt to generate the entire block proof at once, which is less efficient. Additionally, Plonky2 can generate proofs on consumer-grade devices, solving the problem of hardware centralization that often accompanies SNARK proofs.
5. Zero Knowledge Rollup VS Optimistic Rollup
ZK-SNARK and ZK-STARK have become core infrastructure for blockchain scaling projects, especially in the Zero Knowledge Rollup solution. Zero Knowledge Rollup refers to an Ethereum Layer 2 scaling solution that uses zero knowledge proof technology to move all computations off-chain, reducing network congestion. The main advantages of Zero Knowledge Rollup are significantly increased transaction throughput on Ethereum, low transaction fees, and immediate confirmation once transactions are included in the rollup.
In addition to Zero Knowledge Rollup, Ethereum’s L2 scaling solutions also include Optimistic Rollup. In Optimistic Rollup, transactions are assumed to be valid and immediately executed by default. Only when fraudulent transactions are discovered (someone submits fraud proofs) are those transactions revoked. Therefore, the security of Optimistic Rollup is lower than that of Zero Knowledge Rollup. To prevent fraudulent transactions, Optimistic Rollup has a challenge period, during which transactions need to be finalized after the challenge period. This may result in users having to wait for a period of time to withdraw their funds.
When the EVM was initially designed, zero knowledge proof technology was not taken into account. Ethereum founder Vitalik believes that Zero Knowledge Rollup presents technical complexity in the short term but will ultimately prevail over Optimistic Rollup in the scaling war. The following is a comparison between Zero Knowledge Rollup and Optimistic Rollup.
Source: SUSS NiFT, ChatGPT
6. What is the future outlook for zero knowledge proof technology?
The field of zero knowledge proof technology occupies a unique position: in recent years, a lot of effort has been devoted to advancing research in this field, and many achievements are quite new in the fields of cryptography and secure communication. Therefore, many interesting questions still need to be answered by the academic community and developer community. At the same time, zero knowledge proof technology is being used in various projects, demonstrating the challenges and expanding the requirements of zero knowledge technology.
One area of zero knowledge proof technology worth paying attention to is the discussion of post-quantum security. Publicly verifiable SNARKs (succinct non-interactive arguments of knowledge) are a key component of zero knowledge technology. However, most widely used publicly verifiable SNARK schemes are not considered post-quantum secure. For example, Groth16, Sonic, Marlin, SuperSonic, and SLianGuairtan. The mathematical problems these schemes rely on can be efficiently solved with the help of quantum computers, greatly compromising their security in a post-quantum world.
We have found that the academic community is actively seeking quantum-secure zero-knowledge proofs that can be used for various statements without a preprocessing phase. Currently, the most advanced examples of quantum-secure zero-knowledge proofs include Ligero, Aurora, Fractal, Lattice Bulletproofs, and LPK22. Ligero, Aurora, and Fractal are based on hash functions, while Lattice Bulletproofs and LKP22 are based on lattice functions. Both of these functions are considered quantum-secure. It has become a trend to promote these schemes and improve their efficiency.
Another expectation for zero-knowledge technology in the future is its ability to resist attacks and the maturity of related code implementation. With the increase in the amount of code being written, there will be more secure and reviewed libraries and best practices for various zero-knowledge proof technologies. Of course, there will also be more common errors waiting to be discovered and communicated in the future. We expect this field to mature and be widely adopted, working towards standardizing protocols and ensuring interoperability between different implementations. A project called ZKProof has already started doing this.
Another trend that will continue to exist in the zero-knowledge technology community is the work on efficient algorithms and possible specialized hardware. In recent years, we have seen a reduction in proof size and increased efficiency for both provers and verifiers. Advances in algorithms, specialized hardware, and computational optimization may lead to faster and more scalable implementations.
While the efficiency of existing algorithms is beneficial for future zero-knowledge proof technologies, we also expect to see the functionality of zero-knowledge proofs continue to expand. In the past, we encountered many instances when implementing preprocessed ZK-SNARKs. Now we are finding more instances of upgradable ZK-SNARKs. Additionally, the use of some zero-knowledge proof technologies is more due to their conciseness rather than their zero-knowledge capability.
Finally, another trend in zero-knowledge proof technology is the intersection of machine learning and zero-knowledge proofs (ZKML). This idea involves training large language models in a multi-party environment and using zero-knowledge technology to verify computations. This is particularly useful for current artificial intelligence. There is potential for emerging projects in this field.
Conclusion
This article was jointly written by members of the Blockchain Security Alliance. Through this article, we can understand the wide application of zero-knowledge proofs in the blockchain field, the technical path, development trends, and challenges it faces. It is believed that with the development of hardware technology and cryptography, zero-knowledge proofs will achieve more breakthroughs in the future, providing faster and more secure application services for the digital world.
Like what you're reading? Subscribe to our top stories.
We will continue to update Gambling Chain; if you have any questions or suggestions, please contact us!