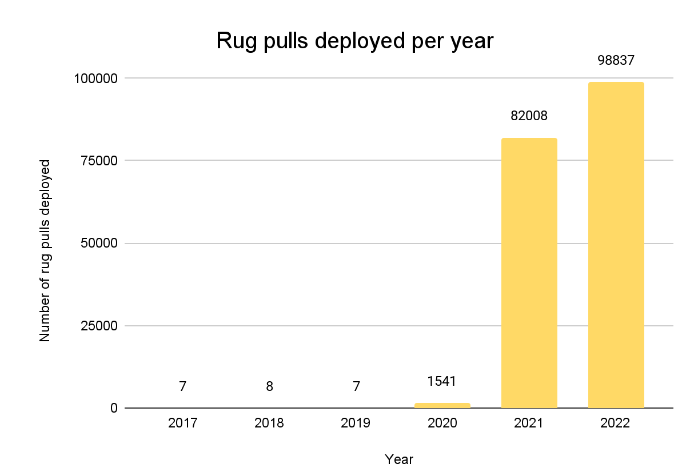
Rug pulls is one of the most common scams in the cryptocurrency industry, and quite frankly, while many have been exposed, many have remained undetected until now. According to solidus labs, at least 188,000 Rugpulls potential scams are deployed on aether place, BNBChain and some header Layer1 blockchains.
Which blockchain has the most RugPulls tokens?
Data show that 12% of Bep-20 tokens on the BNB Chain show signs of fraud, while 8% of Erc-20 tokens on Ethereum show signs of fraud, meanwhile, approximately $910 million of fraud-related ETH is handled through centralized or regulated cryptocurrency exchanges. In October 11 DEFI protocols were attacked, affecting $718 million in encrypted assets, the highest monthly loss of encryption so far this year, according to data from Chainalysis, a blockchain analysis unit.
As one of the largest cryptographic trading platforms in the blockchain ecosystem, the constant addition of new features and expanding user base may be the main reasons why fraudsters and hackers target Binance. Binance appears to be aware of the prevalence of smart contract fraud on its blockchain network and has integrated risk monitoring tools to detect risks in real time and inform users of potential risks, including RugPulls and other scams, so what does RugPulls do? Now let’s analyze it in detail.
Rug Pulls project“Routine”
Rugpulls, also known as the“Fraud Token” or“DeFi scam,” is a program of smart contracts that are carefully coded to steal money from retail investors, often with the goal of:
1. No secondary sales
2. Allow project developers the freedom to mint new tokens
3. Charge buyers 100% of the sales fee
The RugPulls program hides these scripts in tokens, which can be very risky for unsuspecting retail investors to buy. In most cases, RugPulls tokens look exactly like any other cryptocurrency on the market and“Comply” with the blockchain’s homogeneous tokens standard, but the real problem lies deeper in the smart contract source code.
Since the birth of bitcoin, the cryptocurrency industry has become more and more mature, while fraudsters have also figured out the bottom line of cryptocurrency, the underlying intelligent contract, which records trading conditions and rules on the constrained block chain, can be modified substantially. To enforce RugPull, fraudsters often embed malicious rules in smart contracts in a hard-coded manner that not only gives them extra power, but also robs buyers of their basic rights. Typically, fraudsters start the RugPulls project after deploying one or more vulnerable tokens.
When the token is deployed, the fraudster creates a pool of liquidity on a decentralised exchange (Dex) and then trades the token against other“Legitimate” cryptocurrencies. Next, they will artificially inflate the value of tokens by churning out trading volumes that will eventually attract retail interest.
In addition to these“Conventional tools”, the RugPulls project may also“Wrap” its legitimacy in ways such as:
1. Create fake websites and fake project roadmap
2. Share fake partnerships and put up fake“Avatars” of well-known developers
3. Place ads on Twitter, Discord, Telegram, or other social media
As more and more people buy RugPull project tokens, the fraudsters behind the project will start contemplating selling, and once enough users buy the tokens, they quickly sell tokens and exchange them on decentralized exchanges for other cryptocurrencies, such as the ETH and USDT. A large sell-off in a short period of time would bring the tokens price to zero quickly, and the RugPull plot would succeed.
Rugpulls coin fraud type inventory
There are many ways for fraudsters to deploy malicious code in RugPulls’ smart contracts, but there are three main types of RugPulls in the market today:
Hide the deployment honeypot
2. Hide the function of making secret tokens
3. Hide the back door of balance modification
Honeypot vulnerabilities usually prevent tokens buyers from reselling, and only developers can sell their own cryptocurrencies, ordinary investors are often told that a transaction can not be made because of an undefined error; it may be that one of the tokens you are exchanging has a problem. Honeypot scams often lead to a rise in the price of tokens in a short period of time, which in turn induces more unsuspecting users to buy them. A typical example is SQUID Game Token (SQUID) , the project used the name of the Netflix hit“Squid Game” to attract a lot of people to buy it, but the team built a honeypot vulnerability into the smart contract, squid Game Token looked like a promising cryptocurrency, with more than $3.36 million in funding coming in just a few days after launch, but it was eventually looted by the project. As of October 25,2022, there were about 96,008 token items on the market with honeypot vulnerabilities, according to the data.
Counterfeiting is one of the most common methods used by fraudsters, who grant one or more“External-owned accounts”(eoas) specific permissions, allows them to mint new tokens using a hidden feature in the token contract. When a fraudster successfully invokes the coinage function, there will be a large number of tokens that will be dumped on the market, resulting in other holders of tokens being devalued or even rendered worthless. Figures show that as of October 25,2022, there were about 40,569 items in the market with hidden coin-making functions.
The deployment balance modification backdoor is similar to the deployment of private tokens, where fraudsters grant one or more“External-owned accounts (eoas)” specific permissions to modify tokens holders’ balances, when the external-ownership account (EOA) sets tokens holders’ balances to zero, they can not sell withdrawals, and fraudsters can remove liquidity or mint/sell tokens to exit.
Summary
Encryption scams are on the rise and, to make matters worse, many remain undetected. Investors need to assess the risk of encryption fraud when choosing encryption projects, and regulators should step up efforts to prevent harm to consumers, this will ultimately lead to further improvements in market integrity, transparency and consumer protection standards.
Like what you're reading? Subscribe to our top stories.
We will continue to update Gambling Chain; if you have any questions or suggestions, please contact us!